Vpn в каждый дом или как приручить дракона
Содержание:
- Linux and Container Distributions
- Making a Data-Driven Decision
- Managed Elements of the Worker Nodes
- What’s New
- Where to Open Tickets
- Plans and Pricing
- Choose a plan
- Choose a datacenter region
- Droplet Plans for DigitalOcean Kubernetes
- Shared CPU vs. Dedicated CPU
- Limits
- Known Issues
- Limits
- Plans and Pricing
- Authentication
- Features
- Evaluating Connectivity From an External Source
- Choose an image
- Finding Firewall Information
- Help with DigitalOcean Two-Factor Authentication (2FA)
- Plans and Pricing
Linux and Container Distributions
We offer the following versions of these Linux and container distributions:
| Ubuntu | Debian | CentOS | Fedora | FreeBSD | RancherOS | CoreOS (via the API) |
|---|---|---|---|---|---|---|
| 20.04 (LTS) x64 19.10 x64 18.04.3 (LTS) x64 16.04.6 (LTS) x64 16.04.6 (LTS) x32 | 9.12 x64 10.3 x64 | 8.1 x64 7.6 x64 6.9 x64 6.9 x32 | 32 x64 31 x64 30 x64 | 12.1 x64 zfs 12.1 x64 ufs 11.3 x64 zfs 11.3 x64 ufs | v1.5.5 | 2512.3.0 (stable) 2513.1.0 (beta) 2514.0.0 (alpha) |
Tags
Tags are custom labels you apply to Droplets that have multiple uses:
-
Filtering. Tagging multiple Droplets with the same label lets you organize your resources and view a filtered list of Droplets that share that particular tag.
-
Automatic inclusion in firewall rules and load balancer backend pools. Automatically include Droplets in a firewall or load balancer configuration by tag, minimizing administration overhead when adding new Droplets to your infrastructure.
-
API call execution on multiple Droplets at once. Initiate an action across all Droplets with the same tag using the DigitalOcean API. Identifying groups of Droplets and administering all of them at once reduces the time required to manage resources.
Floating IPs
DigitalOcean Floating IPs are publicly-accessible static IP addresses that you can assign to Droplets. A floating IP provides an additional static address you can use to access a Droplet without replacing or changing the Droplet’s original public IP address.
Block Storage Volumes
DigitalOcean Block Storage is a flexible, convenient way of managing additional storage (in units called volumes) for your Droplets. Volumes are independent resources that you can move between Droplets within the same region. You can increase the size of a volume without powering down the Droplet it’s attached to. They’re most useful when you need more storage space but don’t need the additional processing power or memory that a larger Droplet would provide,
Firewalls
DigitalOcean Cloud Firewalls are a free, network-based, stateful firewall service for your DigitalOcean Droplets. They block all traffic that isn’t expressly permitted by a rule. You can define the Droplets protected by a firewall individually or by using tags.
Load Balancers
DigitalOcean Load Balancers are a fully-managed, highly available load balancing service. Load balancers distribute traffic to groups of Droplets, which decouples the overall health of a backend service from the health of a single server to ensure that your services stay online.
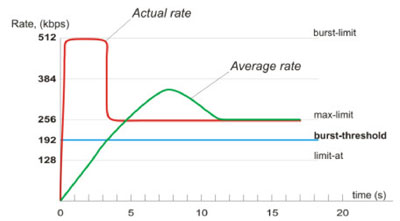
Making a Data-Driven Decision
Before settling on a particular Droplet type, we recommend benchmarking and load testing your workload to see how it performs under simulated load. For bursty apps or batch jobs, look at resource usage when load is at its expected peak, especially when using shared CPU Basic Droplets. If you notice that your app’s performance is too variable for your production needs, consider a Droplet type with dedicated vCPUs.
CPU and RAM
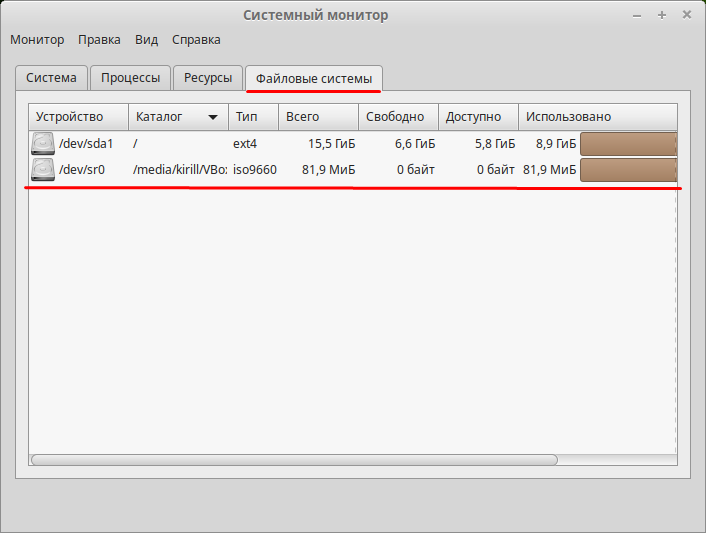
Using Droplet graphs, you can get more information on your Droplet’s CPU load and memory usage:
-
If your Droplet has high CPU usage most of the time and also significant memory usage, consider scaling both vCPUs and memory and using a balanced General Purpose Droplet.
-
If your Droplet has high CPU usage most of the time but very low memory usage, you might be able to save money with a CPU-Optimized Droplet.
-
If your Droplet has high memory usage most of the time (potentially maxing out and swapping to disk) but low or moderate CPU usage, consider scaling memory and using a Memory-Optimized Droplet.
-
If your Droplet has low to moderate CPU or memory usage most of the time but sometimes bursts up and hits resource limits, consider shared CPU Basic Droplets and scale the limiting resource accordingly.
Disk
All DigitalOcean Droplets include variable amounts of local solid state disk (SSD) storage. If you need additional storage, you can use network-attached block storage to attach additional volumes to a Droplet, or use Spaces object storage to offload files and accompanying metadata.
There is some performance penalty when using network-attached storage. If you need the additional input/output operations per second (IOPS), consider scaling your Droplet to a larger size for additional local SSD storage.
Network
Droplets include unlimited free inbound data transfer and some amount of free outbound data transfer, depending on the Droplet instance type and size. Depending on your workload type and bandwidth usage, you could scale your Droplet to take advantage of additional free outbound data transfer.
Monitoring provides graphs and alert policies to monitor both disk and bandwidth, much in the same way you’d monitor CPU and memory usage.
Managed Elements of the Worker Nodes
Worker Node Configuration
You can add more workers and recycle them in the control panel by using the API
or . Once you’ve added them, we manage their configuration, including
the:
- Operating system
- Installed packages
- File system
- Local storage
- Docker daemon configuration
- Machine size
While it is technically possible to access and alter the worker nodes at this time, your changes will be overwritten by the reconciler and will not persist. In the future, you may not be able to change them at all.
Automatic Application of Labels to Nodes
DigitalOcean will apply the following labels to nodes, and their presence is
enforced by the reconciler:
Custom node pool labels can be set through the .
Worker Node Firewalls
When you create a cluster, we automatically create a cloud firewall named concatenated with the cluster name. Its rules open the on the worker nodes. Currently, you cannot close them.
We manage this firewall, which appears in the control panel. While it is possible to alter it manually in the control panel, any changes you make will be overwritten during reconciliation.
The default ports are more than sufficient for most use cases, but if you need to, you can open additional ports. To do so, manually create a new DigitalOcean Cloud Firewall and associate it with the cluster using its specific tag, where is the cluster’s UUID from or the URL in the control panel.
DigitalOcean Infrastructure Components
Some DigitalOcean products integrate natively with Kubernetes clusters directly from the Kubernetes manifest files, and we manage their integration with the cluster:
-
You can add DigitalOcean block storage volumes by creating a PersistentVolumeClaim as part of your deployment.
-
You can add a DigitalOcean Load Balancer by adding a service type to your deployment.
You should not manage these DigitalOcean resources through the control panel or API because any changes you make to Kubernetes clusters outside the cluster’s configuration will be overwritten by the DOKS reconciler. For example, if you manually delete a block storage volume or load balancer in a Kubernetes cluster from the control panel, it will be recreated during the next reconciliation process and you will still be billed.
What’s New
Upcoming Changes
-
The ability to create new Spaces in FRA1 remains disabled while we update capacity in this region.
-
charges will now appear on invoices. The first charge will appear on July 2020 invoices for all floating IPs that were not assigned to Droplets during the month of June.
31 August 2020
-
Standard Droplet plans have been replaced with Basic Droplet plans. We have added one new plan, , and deprecated the following plans:
These deprecated plans are now unavailable in the control panel, but you can still create Droplets with those plans using the API or .
4 August 2020
We have released a Droplet metadata endpoint which returns whether or not a Droplet is scheduled for a live migration. The impact of live migrations on Droplets is minimal, so users now only receive direct notifications for migrations that require us to power down a Droplet, which (except in emergencies) we send 7 days in advance.
28 July 2020
On 1 August 2020, Ubuntu 19.10 will reach its end of life and will not receive further updates. Per our image deprecation policy, you can only deploy the Ubuntu 19.10 Linux image via the API starting on 1 August 2020. We will remove the Ubuntu 19.10 image from the platform on 1 September 2020.
For more, see our full release notes.
Where to Open Tickets
-
To report abuse, contact our trust and safety team.
We are committed to a better Internet and take violations of the Rules of Conduct in our Terms of Service agreement from sites we host seriously.
-
For Premier Support or help with large deployments, contact our sales team.
We can support large deployments with migration planning, large volume pricing, Solutions Partner recommendations, and more.
-
If you cannot sign in to your account: use our account recovery form.
Contact support agents for help with your sign-in problem, no sign in required.
-
For account questions and technical problems, you can open a ticket by clicking the support icon in the control panel:
Plans and Pricing
The base rate of a Spaces subscription is $5/month and gives you the ability to create multiple Spaces.
The subscription includes 250 GiB of data storage (cumulative across all of your Spaces). Additional storage beyond this allotment is $0.02/GiB. If you cancel your subscription by destroying all your Spaces, your bill will be prorated hourly.
Bandwidth
Spaces subscriptions include 1,024 GiB of outbound data transfer (from Spaces to the internet), which is shared between all Spaces. Additional outbound transfer is $0.01/GiB. Outbound data transfer is free in the following cases:
- From Spaces in NYC3 to Droplets in NYC1, NYC2, and NYC3
- From Spaces in SGP1 to Droplets in SGP1
- From Spaces in SFO2 to Droplets in SFO1, SFO2, and SFO3
- From Spaces in AMS3 to Droplets in AMS2 and AMS3
- From Spaces in FRA1 to Droplets in FRA1
Inbound bandwidth to Spaces never counts against your Spaces transfer allowance.
Droplets have their own transfer allowance, independent of Spaces. Traffic from Droplets to Spaces does not count against your Spaces transfer allowance (because inbound bandwidth to Spaces is free), but does currently count against your Droplets’ outbound transfer allowance. We’re working on changing this behavior.
Content Delivery Network (CDN)
The Spaces Content Delivery Network (CDN) is available at no additional cost. The transfer allowance that comes with the base Spaces subscription covers both CDN bandwidth and origin bandwidth. Transfer between the origin and the edge servers is calculated as part of the transfer allowance.
Choose a plan
In the Choose a plan section, you choose the amount of RAM, storage space, and CPU cores your Droplet will have.

There are four types of plans:
-
Basic Droplets, a flexible option best for most use cases, like website hosting, staging environments and low intensity compute needs.
-
General Purpose Performance Droplets, a robust option suitable for a wide variety of mainstream, production applications that require a higher ratio of memory to CPU.
-
CPU-Optimized Performance Droplets, best for CPU intensive tasks and projects that require predictable performance or rely on CPU more than RAM or I/O, like batch processing large data sets, large builds, and video encoding.
-
Memory-Optimized Performance Droplets, best for resource-intensive business applications, like high-performance SQL or NoSQL databases, large in-memory caches and indexes, real-time big data processing, and applications with large JVM requirements.
See How To Choose a Droplet Plan for an in-depth guide to choosing a Droplet plan.
Note
For Droplets with less than 3 GB of RAM, we recommend using a 32-bit operating system. Processes require more memory on 64-bit architectures, and on servers with a limited quantity of RAM, any performance benefits from a 64-bit OS are offset by having less memory available for buffers and caching.
Choose a datacenter region
In the Choose a datacenter region section, select the region where you want to create your Droplet.
A good default is selected for you, but for the best performance and minimal latency, choose the datacenter nearest to you and your users. You can also make a decision based on which products and features are available in which regions.

The create page greys out datacenters that are incompatible with your selected configuration and add a tooltip with an explanation. For example, if you add a block storage volume to your configuration, you won’t be able to create your Droplet in a datacenter that doesn’t support volumes.

Droplet Plans for DigitalOcean Kubernetes
If you use Droplets to run a container cluster with DigitalOcean Kubernetes, there are different considerations to choosing the best Droplet plan. You can combine several different Droplet instance types to create a set of resources sized optimally for your running containers.
Many container clusters, like Kubernetes, have advanced scheduling features that let you specify the Droplets your containers will run on. For example, if you are running a memory-bound data processing app, you can schedule that workload to a group of Memory-Optimized Droplets to avoid hitting memory limits and swapping to disk.
Learn more in Advanced Scheduling in Kubernetes.
-
A Droplet is a virtual machine (VM) that is allocated resources, like CPU, RAM, and disk storage, from a physical host.
-
A hypervisor, also known as a virtual machine monitor, makes sure that the multiple Droplets running on a physical host each receive their virtual resources, like vCPU.
-
A vCPU is a unit of processing power corresponding to a single hyperthread on a processor core. A modern, multicore processor has several vCPUs.
The Droplet plan you choose determines the amount of resources allocated to the Droplet. Resources like RAM, disk storage, and network bandwidth are always dedicated, but you can choose between shared CPU and dedicated CPU plans for dedicated vCPU.
Dedicated CPU Droplets have guaranteed access to the full hyperthread at all times. With shared CPU Droplets, the hyperthread allocated to the Droplet may be shared between multiple other Droplets. When a shared CPU Droplet experiences heavier load, the hypervisor dynamically allocates more hyperthread(s) to it.
However, the amount of CPU cycles available for the hypervisor to allocate depends on the workload of the other Droplets sharing that host. If these neighboring Droplets have high load, a Droplet could receive fractions of hyperthreads instead of dedicated access to the underlying physical processors. In practice, this means that shared CPU Droplets can have access to full hyperthreads, but it’s not guaranteed.
Limits
-
We do not support VPC networks between resources in different datacenter regions.
-
You cannot migrate load balancers or Kubernetes clusters between VPC networks. Droplets can be migrated between networks , and databases can be directly migrated in their .
-
VPC network ranges cannot overlap with the ranges of other networks in the same account. The IP ranges available for VPC networks are the same as those outlined in RFC 1918.
-
VPCs do not support multicast or broadcast.
-
Resources do not currently support multiple private network interfaces and cannot be placed in multiple VPC networks.
-
We reserve a few addresses in each VPC network and subnet for internal use, including the network ID and the broadcast ID.
-
The , , and IP address ranges are reserved in all regions for DigitalOcean internal use. We also reserve the following IP ranges in the these regions:
Region Reserved Range AMS1 10.11.0.0/16 AMS2 10.14.0.0/16 AMS3 10.18.0.0/16 BLR1 10.47.0.0/16 FRA1 10.19.0.0/16 LON1 10.16.0.0/16 NYC1 10.10.0.0/16 NYC2 10.13.0.0/16 NYC3 10.17.0.0/16 SFO1 10.12.0.0/16 SFO2 10.46.0.0/16 SFO3 10.48.0.0/16 SGP1 10.15.0.0/16 TOR1 10.20.0.0/16
Known Issues
-
Space delete actions do not include the correct IP address that conducted the action in an account’s security history.
-
Uploading hundreds or thousands of files via may not complete reliably. For this use case, use s3cmd or other third-party tools.
-
In the API, pagination does not work.
-
Uploading files and folders with spaces in their name is not supported, but when you upload using the drag and drop feature, they will upload successfully.
-
You cannot currently create wildcard SSL certificates using DigitalOcean’s Let’s Encrypt integration. Instead, choose the Bring your own certificate option to add custom wildcard certificates.
-
File metadata headers, like , are not passed through the CDN. Metadata headers are correctly set when fetching content directly from the origin.
-
CDN subdomain certificates can silently fail to upload to the CDN on renewal. This causes the CDN to stop serving assets with SSL once the original certificate expires. Additionally, when this happens, you cannot change the invalid certificate in the control panel.
Our engineers are working on a fix for the certificate renewal uploads and a fix in the control panel to support uploading or selecting a different certificate when a renewed certificate upload fails.
As a workaround, you can . You can also open a support ticket for help.
Limits
-
Spaces have the following request rate limits:
-
750 requests (any operation) per IP address per second to all Spaces on an account
-
150 s, 150 s, 150 s, and 240 other requests per second to any individual Space
-
2 s per 5 minutes on any individual object in a Space
Applications should retry with exponential backoff on 503 Slow Down errors. If you plan to push more than 200 requests per second to Spaces, we recommend using the Spaces CDN or creating more Spaces.
-
-
Spaces have the following upload rate limits in AMS3:
-
Uploading up to 150 GB of data in 24 hours is unthrottled.
-
If uploads to a Space exceed 150 GB of data in 24 hours, that Space’s upload bandwidth is gradually throttled until its 24-hour accumulated uploads return to 150 GB or less.
-
If uploads to a Space exceed 270 GB of data in 24 hours, that Space’s upload bandwidth is set to 1MB/s for the next 24 hours.
-
-
Spaces have the following file size limits:
-
requests can be at most 5 GB
-
Each part of a multi-part upload can be at most 5 GB
-
Each part of a multi-part upload must be at least 5 MiB, except for the final part
-
Multi-part uploads have a 10,000 part limit
-
The maximum supported total size of a multi-part upload is 5 TB
-
-
DigitalOcean’s internal DNS infrastructure has rate limits in place to limit the impact of abusive actors. If you are making a large number of requests, we recommend implementing recursive DNS caching.
-
Sharing ownership of Spaces is currently per account, not per Space.
-
While you can set permissions for all the files in a folder, currently you’ll need to use a third-party client to set permissions recursively.
-
Spaces currently do not support tags.
-
You cannot delete more than 10,000 files from a Space at once via the control panel. You can use the API or delete fewer files at a time.
-
The Transmit v. 5.0.5 release solved some compatibility issues, but it is not yet fully compatible with Spaces. Please use Transmit 4 as a workaround.
-
In the 2+ week period during which a Space is pending destruction, you cannot reuse that Space’s name. If you need to recover a Space that is pending destruction, open a support ticket.
-
You cannot secure a CDN’s subdomain with a custom wildcard SSL certificate that is already being used elsewhere in your account. Instead, you’ll need to add a new custom certificate during the custom subdomain set up for your CDN.
-
If you include a period, , in the name of a Space, SSL wildcard certificates will not match. We recommend against using periods in the names of Spaces.
Plans and Pricing
We offer four different kinds of Droplet plans: one shared CPU plan and three dedicated CPU plans.
| Droplet Plan | CPU | Range of Resources | RAM-to-CPU Ratio | Processor |
|---|---|---|---|---|
| Basic | Shared | 1 — 32 vCPUs1 — 192 GB RAM | Variable | |
| General Purpose | Dedicated | 2 — 40 vCPUs8 — 160 GB RAM | 4 GB per vCPU | Intel Xeon Skylake (2.7 GHz, 3.7 GHz turbo) |
| CPU-Optimized | Dedicated | 2 — 32 vCPUs4 — 64 GB RAM | 2 GB per vCPU | Intel Xeon Broadwell (2.6 GHz)Intel Xeon Skylake (2.7 GHz, 3.7 GHz turbo) |
| Memory-Optimized | Dedicated | 2 — 32 vCPUs16 — 256 GB RAM | 8 GB per vCPU |
Learn more about shared CPU vs. dedicated CPU and the best use cases for each kind of plan in Choosing the Right Droplet Plan. You can view all available Droplet plans on the .
Note
You are still billed for Droplets that are powered off because the compute resources for the Droplet stay reserved on the hypervisor, even when they are not in use. To end billing, destroy the Droplet.
Bandwidth
Each Droplet includes free outbound data transfer, starting at 1000 GiB/month and scaling up. Outbound data transfer is shared between all Droplets each billing cycle. Additional transfer is billed at $0.01/GiB, but most users don’t exceed the amount included with their Droplets.
You can view your accumulated monthly transfer allowance on your account’s billing page in the Droplet transfer section. For an in-depth description of how data transfer accrual works, read our detailed bandwidth billing page.
Authentication
In the Authentication section, you choose the method you want to use to log in to your Droplet. There are two options:
SSH keys, which provide more security than a password.
Password, which allows you to create your own password for the new Droplet.

If you choose to use SSH keys, you need to select at least one key to add to the Droplet. Any keys you’ve already uploaded to your DigitalOcean account are listed.
Check the boxes next to the existing keys you want to add to the Droplet, or check Select all to add every key on your account. You can also click New SSH Key to upload a new key to your account from the create page.
Once you create and upload an SSH key to your DigitalOcean account, it remains available for you to add to any new Droplets you provision in the future.
Features
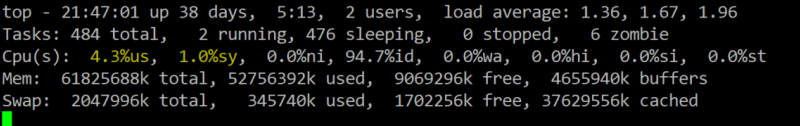
Additional Droplet Graphs
Droplet graphs are a visual representation of system-level metrics to provide a high-level overview of resource usage. This can help you understand how your resource usage is changing over time and how different resource levels correlate.
By default, Droplet graphs only display information about public and private bandwidth usage, CPU usage, and disk I/O. With DigitalOcean Monitoring, you gain access to additional metrics, including load average (1-, 5-, and 15-minute), memory usage, and disk usage.
Metrics Agent
The DigitalOcean metrics agent is an open-source Go utility that forwards basic metrics about your Droplet to the DigitalOcean metrics backend. It currently supports the following operating system versions:
- Ubuntu 14.04 and higher
- CentOS 6 and higher
- Debian 8 and higher
- Fedora 27 and higher
There is also the option to .
What Can the Metrics Agent Access?
The metrics agent service runs as an unprivileged user with access to only three directories:
- : Where the metrics agent collects data about the current state of the system
- : Where the metrics agent writes its authentication information
- : The binary’s home directory
The metrics agent also reports the process names to the metrics endpoint, which DigitalOcean uses internally in aggregate to help guide product priorities. It does not report on environmental variables or process arguments to avoid exposing potentially sensitive information. However, you can still opt out of process name collection.
How Does the Metrics Agent Send Metrics?
The DigitalOcean metrics agent uses ports 80 and 443 for outgoing data. Inbound access is not required. Since the metrics agent only uses the ports for outbound data, you can safely run a web server without interference.
Port 80 is used to contact the DigitalOcean metadata service to obtain an authentication token. The metrics agent uses this token to authenticate to the metrics backend and encrypt its transmissions.
Evaluating Connectivity From an External Source
Gathering information about the state of your DigitalOcean Cloud Firewall rules and any host-based firewall rules is important to understand the intended network access. However, it’s also important to validate the actual traffic filtering behavior with tests.
By installing tools like on an outside host, we can check which ports we can connect to on our Droplets. If you have Firewall rules that limit access based on the originating host, you may have to install on multiple machines (those in the allowed group and those outside) in order to get a complete picture.
Note
If you only wish to allow connections from certain hosts, targeting Firewall rules with tags will make management and testing significantly simpler. You can install on a single test Droplet and then add or remove tags from that server to change which rules match the connection request.
For more complete information about scanning hosts with , follow our guide on How To Test your Firewall Configuration with Nmap and Tcpdump.
Installing Nmap
To start, you will need to install on a Droplet that is not a part of the infrastructure you wish to scan.
To install on an Ubuntu or Debian testing Droplet, type:
To install on a CentOS testing Droplet, type:
You should now be able to check the target infrastructure.
Scanning TCP Ports
Once the scanner is installed, you can scan for open TCP ports by typing:
The scan will attempt a SYN TCP connection to every port on the target Droplet. If you want to limit the number of scanned ports in order to speed up the scan, you can replace the option with a range or sequence of ports instead:
If you remove the option entirely, will scan the 1000 most common ports, which is good when you have limited time or are only interested in the state of common service ports:
If you have rules that limit traffic according to origin, make sure to run this test against your target infrastructure from a host where connections are supposed to be allowed and again from a host where connections are supposed to be denied.
Scanning UDP Ports
Because UDP is a connectionless protocol, scanning with UDP is significantly more error prone and time consuming than TCP scans. Since the Cloud Firewalls block traffic by silently dropping offending packets, it is difficult or impossible to distinguish between open and filtered UDP ports by port scanning.
This is beneficial in most situations as it makes it more difficult for outside parties to understand the services running on your infrastructure. However, this interferes with your ability to audit your UDP Firewall rules and so it cannot be used reliably for this purpose.
You can read more about the limitations of UDP scanning in our .
Choose an image
In the Choose an image section, you choose the image your Droplet will be created from. Initially, you can choose from four categories of images:
-
Distributions are basic Unix-like images with no additional software, including Ubuntu, Fedora, Debian, CentOS, and FreeBSD.
-
Container distributions include RancherOS.
-
Marketplace images include pre-configured applications, like Docker, WordPress, or LAMP, to help simplify getting started.
-
Custom images are Unix-like images that you create and upload to your DigitalOcean account.

Once you start using Droplets, you can make backups and take snapshots of them. You’ll see tabs for Backups and Snapshots on the Droplet creation page when you start using those features, and you can choose those images as the foundation to create new Droplets.
-
Snapshots are images taken on demand and are useful to manually back up or reproducibly create Droplets.
-
Backups are system-level backups automatically taken once a week. The last 4 weeks of backup images are retained, and you can use them as a basis to rebuild an existing Droplet.

Finding Firewall Information
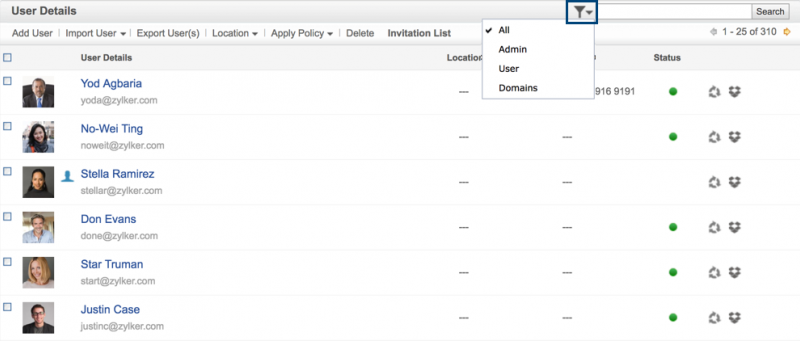
The first step in diagnosing problems in your Firewall policy is to understand the which rules are being applied. The control panel contains information about individual Firewalls as well as the combined rule set that applies to each Droplet.
Displaying Information About All Firewalls
To view all of your Firewalls in the DigitalOcean Control Panel, click on the Networking item in the main navigation pane and then select the Firewalls subitem. The Firewall index page lists basic information about each of your Firewalls like the number of Droplets it applies to, the number of rules it contains, and when it was created:

Clicking the name of a Firewall takes you to the Firewall detail page where you can see the policy’s individual rules and the Droplets it targets. This is also where you can add and remove Droplets and tags.

Reviewing the rules applied by each of your Firewalls can provide an overview of the types of network policy being enforced on your infrastructure as a whole.
Displaying the Firewall Policy Affecting an Individual Droplet
The Firewall index and detail pages are not the best place to look if you are interested in the policy affecting an individual Droplet. Instead, check the Droplet’s detail page.
From the Droplets item in the main control panel navigation menu, click the Droplet’s name. From there, click Networking in the Droplet menu. Towards the bottom of the page, a section called Firewalls lists the Firewalls that target the Droplet. Below, the policies from each of the Droplet’s Firewalls are combined into a comprehensive table:

These inbound and outbound rules represent all of the traffic allowed through the Firewall for the Droplet. If you are experiencing issues with connectivity to your Droplet after applying a Firewall policy, this is a good place to look.
Help with DigitalOcean Two-Factor Authentication (2FA)
I can’t access my 2FA device
If you’ve successfully entered your username and password and are experiencing an issue with two-factor authentication, you can disable 2FA using your backup method (backup codes or SMS).
Backup Codes
Search your computer for the backup recovery codes text file, which by default would be called . If you find that file, use one of the codes by logging in to the control panel and clicking Enter a recovery code at the bottom of the Two-factor authentication screen. Remember that if you successfully use the code, you cannot use it again, so you may want to mark it as used or delete it from the file.

SMS Codes
Log in to the control panel and enter your account credentials. click Send an SMS instead at the bottom of the Two-factor authentication screen.

You are prompted to enter a verification code, which you receive via SMS at the phone number you entered when you configured SMS as your backup method.
See How to Manage Two-Factor Authentication more information on 2FA, including how to update your device.
They will need additional information to verify that you are the account owner, so be prepared with a photo of your government-issued ID (e.g. passport, driver’s license, military ID). The name on ID in the photos must match the name for the account information that we have on file.
Plans and Pricing
The cost of a DigitalOcean Kubernetes cluster is based on the cluster’s resources:
-
Nodes are built on Droplets. The master node is fully managed by DigitalOcean and included at no cost. Worker nodes are charged at . Both Basic and CPU-Optimized Droplet plans are available for worker nodes.
-
Integration with DigitalOcean Load Balancers is charged at .
-
Integration with block storage volumes is charged at .
All charges for Kubernetes clusters appear in the Kubernetes section of monthly invoices.
Bandwidth
Outbound data transfer is shared between all Droplets, including Kubernetes worker nodes, so bandwidth for Kubernetes cluster worker nodes is charged at the same rate as .
You can view your accumulated monthly transfer allowance on your account’s billing page in the Droplet transfer section. For an in-depth description of how data transfer accrual works, read our detailed bandwidth billing page.